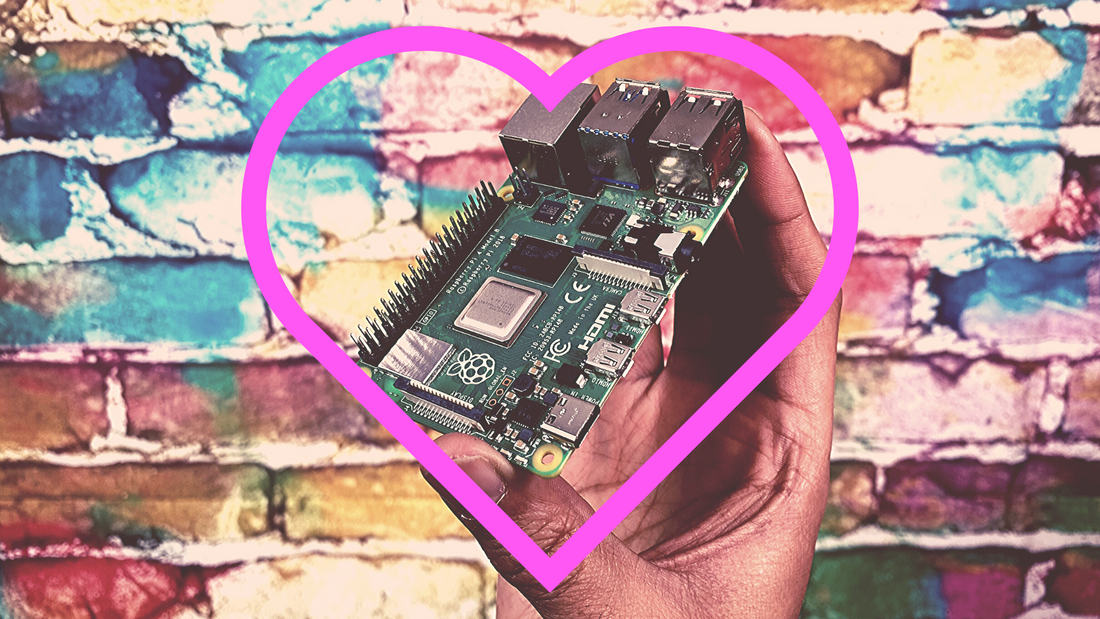
Here at notiaPoint, we just released the Pi’d Hacker Experience that teaches you essential cybersecurity and hacking skills using a miniature computer known as the Raspberry Pi.
You probably asked yourself, “What’s that? What the heck is a Raspberry Pi? How is that going to help me learn cybersecurity?”
Back to the Basics
Cybersecurity is all about making technology more secure. The heart of technology all starts with a chip, meaning that the foundation of cybersecurity can be learned through understanding how chips work. When we know how the hardware works, we begin to understand technology enough to secure it.
Since all modern internet-accessible technologies contain a chip, they are all prone to the same core vulnerabilities.
This matters because if you can figure out how to hack a Raspberry Pi, you can learn how to hack anything!
Whether you’re just learning hacking skills or want to become more comfortable on Linux, or you’re a contract penetration tester looking for advanced solutions, Raspberry Pis can do it all.
Creators in the technology space have been using the Raspberry Pi platform for years to build everything – from network routers to tiny supercomputers and even robotics.
These little computers are incredibly utilitarian and completely customizable and could easily find practical daily use in your home or office. A few practical applications for Raspberry Pis include the following:
- Use it to replace your desktop computer.
- Turn it into a media streaming center.
- Play old-school games on it with an emulator.
- Stream new PC games with Steam Link.
- Give network-wide access to your old USB printer.
- Build a network-wide ad blocker.
Let your imagination run wild! Literally the sky's the limit with the Raspberry Pi.
Advanced Uses for Raspberry Pi
As you grow your skills and cybersecurity knowledge with notiaPoint’s Pi’d Hacker Experience, you’ll also discover the Pi’s more advanced cybersecurity applications.
If you are analyzing malware, you don’t want to perform tests on your $2,000 laptop – even running a virtual machine leaves your hardware vulnerable. Use a Pi instead!
If you are pentesting a company’s network, you can deploy multiple Pis from multiple parts of the network and orchestrate all of the pis together at once to perform larger scale attacks and tests.
Raspberry Pis can also be used for easy remote access to provide continued network monitoring. Remote Pis can be set up in multiple offices for secure remote access.
You can also run containers on Raspberry Pi for further data isolation, allowing for highly efficient Pi container architectures that can also be used to increase security.
So there you have it. Like we’ve said before, the Raspberry Pi is an incredible and incredibly versatile machine.
When you’re ready to get started, check out the Pi’d Hacker Experience.